Tag: container
Swap from Debian to Ubuntu as Linux image on Pixel Slate Chromebook
This might be a little detailed for most, feel free to don your peril-sensitive sunglasses. So, no offence to Debian 9.6 Stretch, but the rest of the fleet runs Ubuntu, which is very similar, but, well, some packages are different. So lets see how we can make the Chromebook run a Ubuntu image and still…
Suicidal clouds cause consternation
Another day another piece of infrastructure cowardly craps out. Today it was Google GKE. It updated itself to 1.11.3-gke.18, and then had this to say (while nothing was working, all pods were stuck in Creating, and the Nodes would not come online since the CNI failed). 2018-12-03 21:10:57.996 [ERROR][12] migrate.go 884: Unable to store the…
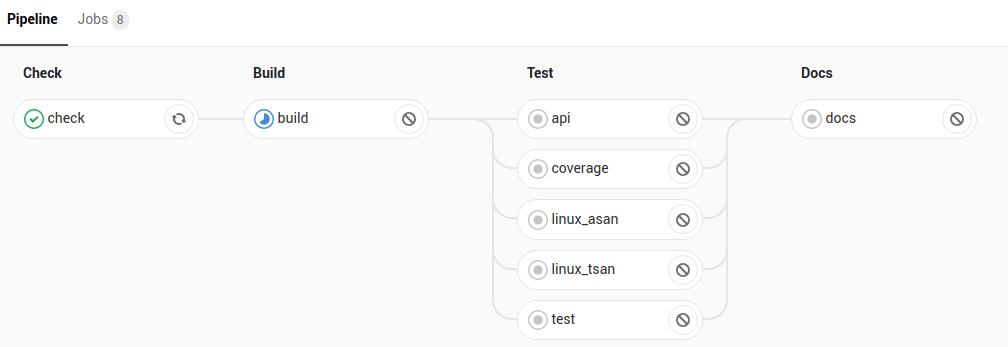
Next Chautauqua: Continuous Integration!
Tomorrow (Tues 27, 2018) we’re going to have the next meetup to talk Continuous Integration. Got a burning desire to rant about the flakiness of an infinite number of shell scripts bundled into a container and shipped to a remote agent that is more or less busy at different hours? Wondering if its better to use…
Separate CI cluster woes: can hierarchical caching help?
So I have this architecture where we have 2 separate Kubernetes clusters. The first cluster runs in GKE, the second on ‘the beast of the basement‘ (and then there’s a bunch in AKS but they are for different purposes). I run Gitlab-runner on these 2 Kubernetes clusters. But… trouble is brewing. You see, runners are…
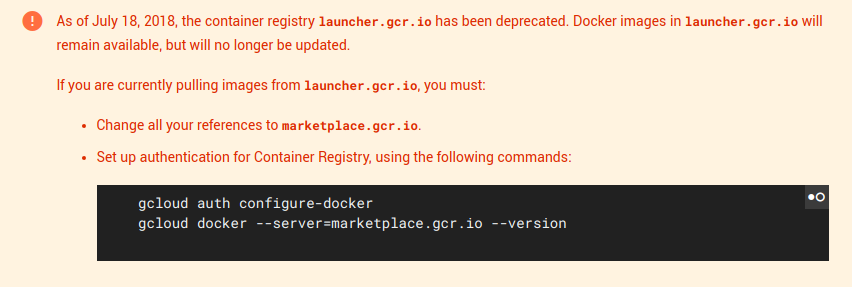
PSA: launcher.gcr.io is not being maintained
So you might have cut and paste some code from somewhere, maybe an ‘from launcher.gcr.io/debian9’ kind of thing. That’s a good upstream, right? They are maintaining it with a strong CI? When suddenly you read Hmm. Double whammy. You have been relying since 2018-07-18 on something which is not being updated (and daily rebuilding your…