Month: August 2018
Tales from the road: the one with the taco and the shoe-shine.
So I used to frequent Mexico city. On one of my trips there I was going to see someone muy importante. Our local guy was a very good host, would drive me everywhere, make sure I had a good time, etc. On this trip, we had a few minutes to kill in the hotel lobby…
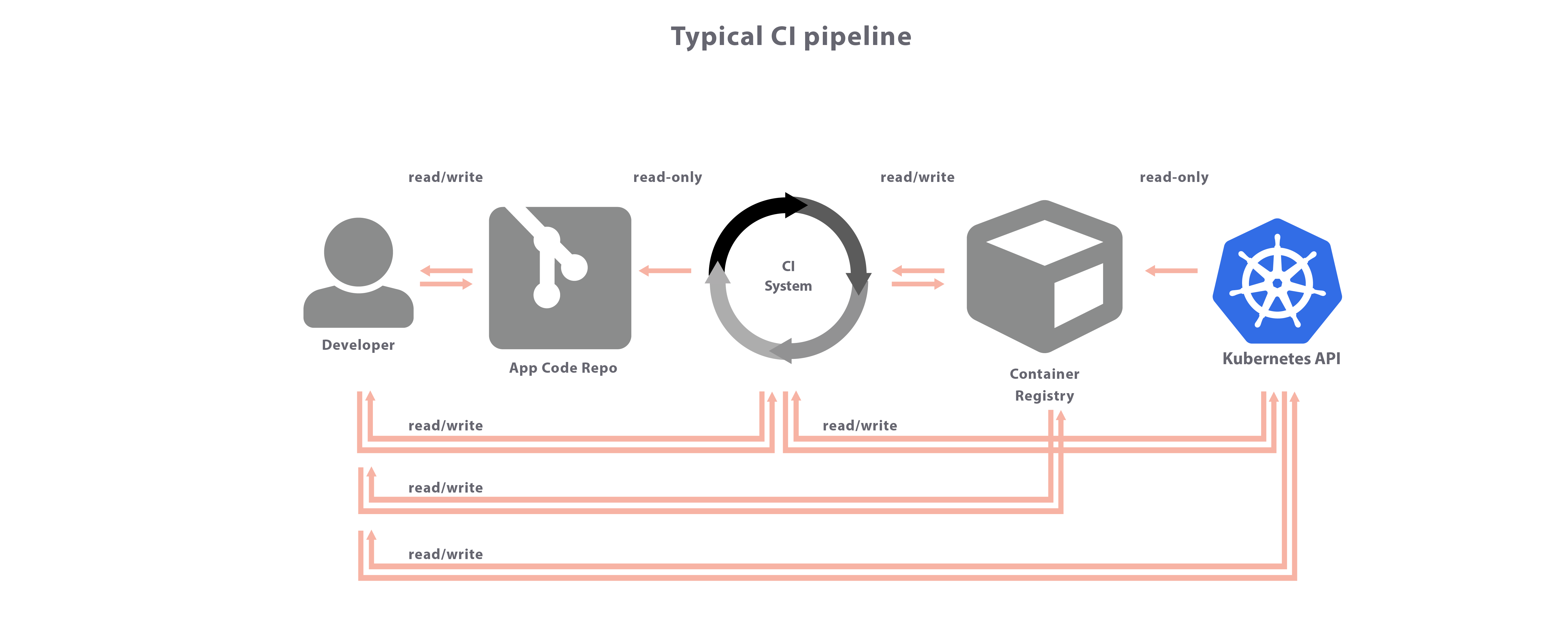
Should I use my CI pipeline to do continuous delivery? A controversy!
I’m using Gitlab, and one of the things they promote is Auto-Devops. In a nutshell, you use the Gitlab-CI as your means from start to finish, starting w/ an idea, through code, unit-test, address-space-tests, dynamic-tests, thread-tests, license-checks, lint, code-format, static scans, … all the way until it lands on a running server somewhere for your…
Tales from the road: of Russia, Google, Trump, search results, and opening a new front
Many years ago Hitler decided to open a 2nd front in World War 2, against Russia. This turned out to be a bad idea for him, but ultimately a good thing for the rest of us. Today we saw a similar issue, Google being accused of search bias is opening a new front, why pick…
Insecure web sites. #tlswallofshame
You’ve no doubt noticed that chrome now marks any non https-site as insecure. Its no longer that ‘https is secure the rest is unspoken’. Its actively insecure. Some sites have no support for https (shame). Some have support, but you have to remember to use that URL (should redirect). But, what is the thinking behind…
Endoscope: snoop around inside your Kubernetes pods
Today I ‘released’ endoscope. This is a tool that solves a couple of ‘simple’ problems: I have a running container in Kubernetes. I wish I could have a shell inside it that is root, but also with a bunch of tools like gdb or ptrace. My container doesn’t allow root or ptrace. I don’t want…