Month: July 2018
Less is more
Less is more. Famous saying, perhaps less well known person (Ludwig Mies van der Rohe). Another way to look at this is “Perfection is achieved, not when there is nothing more to add, but when there is nothing left to take away” (Antoine de Saint-Exupery). Course he also said ‘Dessine-moi un mouton!’ which became a…
Attack of the rack: the killer was in the house!
You know the joke about the crappy horror movie, they trace the IP, its 127.0.0.1, the killer was in the house (localhost)? True story, this just happened to me. So settle down and listen to a tale of NAT, Proxy, Kubernetes, and Fail2Ban (AKA Rack Attack in ruby land). You see, we run a modest…
The agony of NFS: the knife twists a bit more
Recently Google announced Filestore. I was all set to rejoice, after my heartbreaks of recent days. After all, it seemed like NFS might have been the answer for me, but I would have to have it run outside of Kubernetes. So it was with great joy I signed up for the beta program, and even…
Spam sushi in a vending machine? People feeding trash pandas at underpasses? Must be in California!
So I’m here at Google Next this week. Cloud cloud cloud, security security security, that sort of thing. Question 1. Would you buy this ‘spam musibi‘ from this vending machine? Or you’d rather have that tasty-looking turkey? Or that delicious looking hot dog? Keep in mind there is no microwave around, so that cold vended…
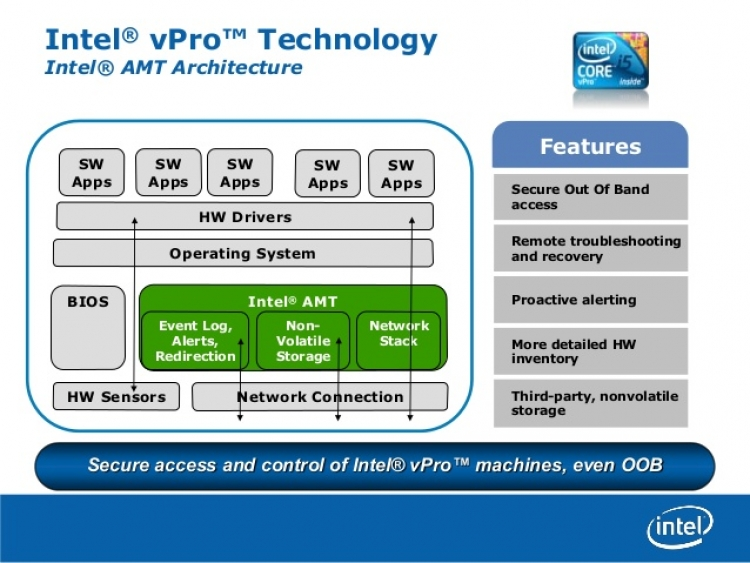
Got Intel? Got security hole
Well this is awkward. That Intel Management Engine (AMT) that you can’t disable. That one that runs even when your machine is turned off. The one that runs with highest privilege, no oversight, outside your operating system. The same one that everyone wonders, just what is in there. Turns out, from the security audit, some…