Tag: society
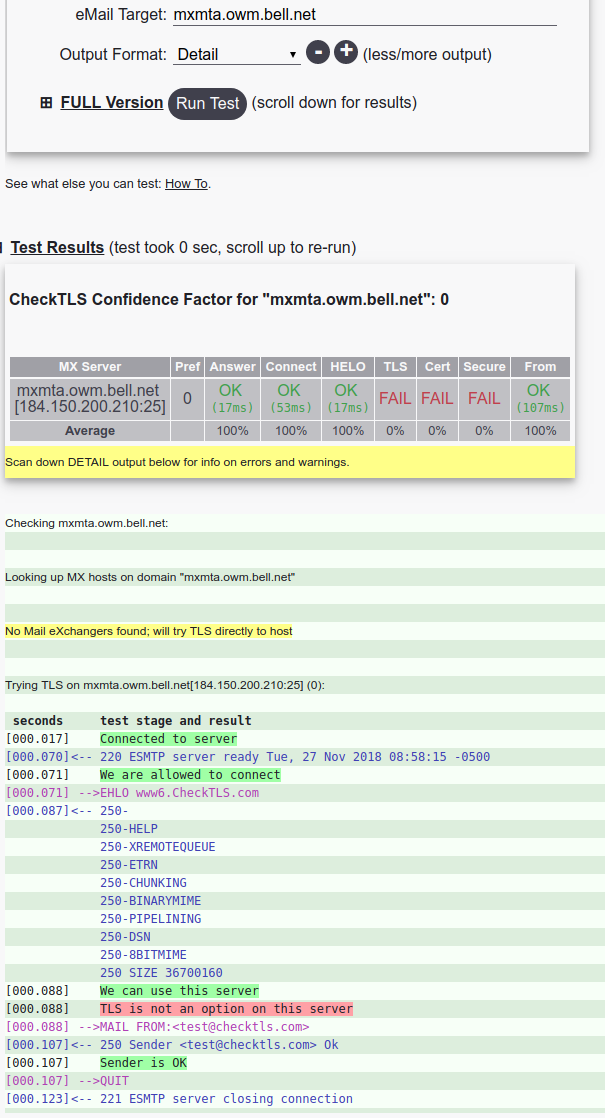
Why does Bell Canada not allow encrypting your email in transit?
Hint: you want your email to be encrypted in transit. Now, lets take a look at some stats. From my earlier post about ‘Why is Canada less encrypted than the US‘?, and from Google’s Transparency Report, we dig into Sympatico. This is Bell Canada‘s brand for Internet. We see that there is no encrypted email exchanged…
Do the phish scammers care more about your security than you do?
Phishing has hit the halfway point on encryption. This means that being TLS-encrypted is no indication a site is real or not (its an indication that it is exactly what it says it is, but not what it might appear as). Ironically, they might be stronger than the average web site. If we look at…
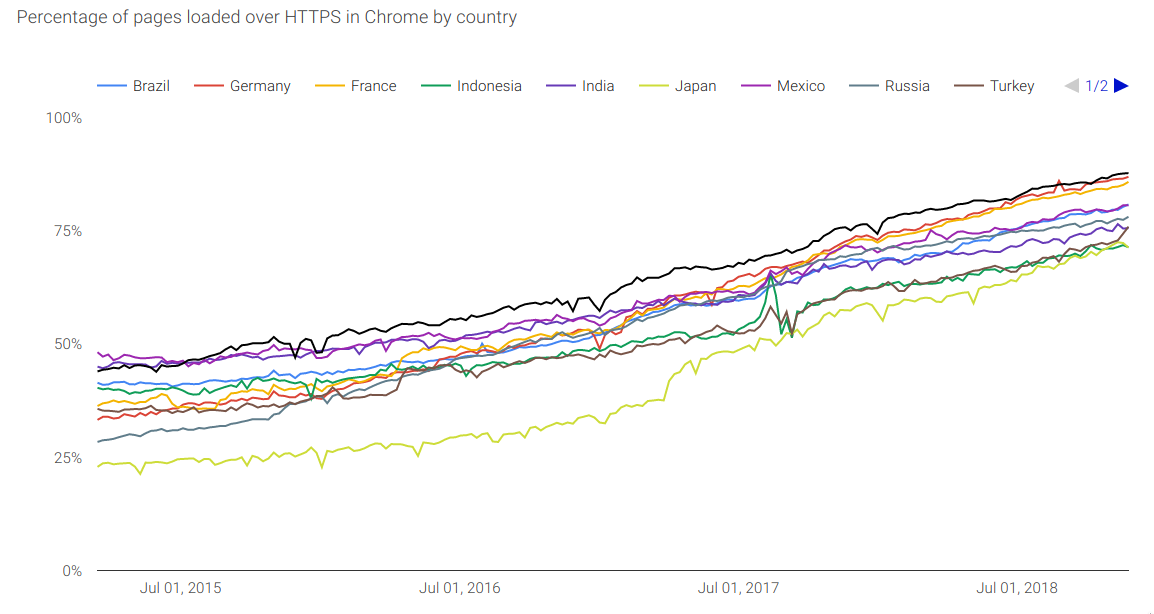
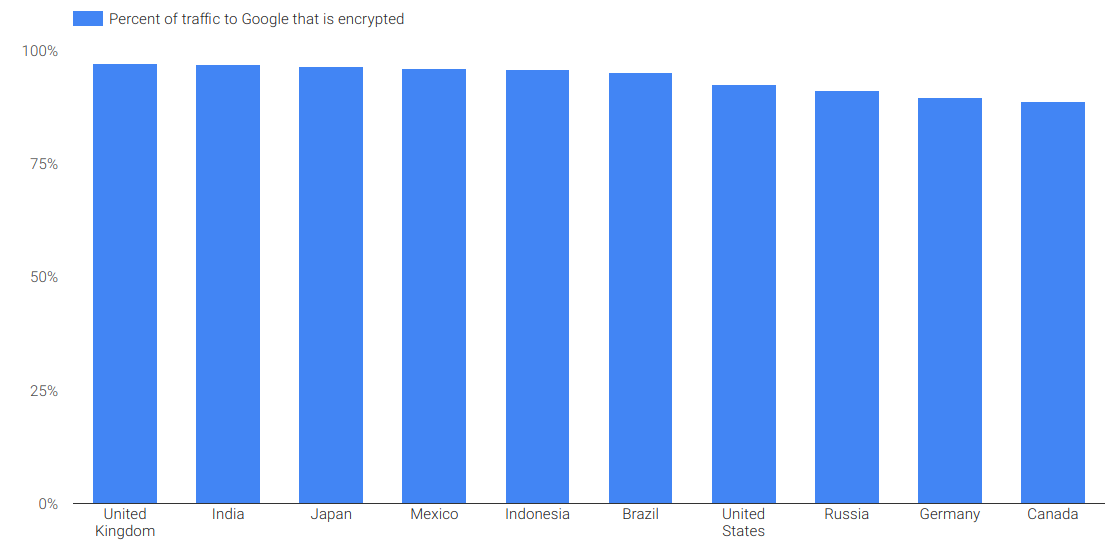
Why is Canada worse than the UK and US for encrypted web?
Courtesy of our friends @ Google and their Transparency Report we see that Canada is 89% encrypted to Google. Good, but not great when you realise the UK is 97% encrypted. What could drive this difference? I would think device-types and ages would be similar. This traffic is a bellwether of other encrypted traffic, and we…
Its looking like HTTP/3 will be all encrypted and all UDP, all the time
I started my web-ish life with HTTP 0/9. It was the dialect that ‘escaped’ from Cern. Soon after HTTP/1.0 came along, and then 1.1. And we stuck on 1.1 for a long time (more than 2 decades). And then HTTP/2 came along, and it was great. 100% encrypted, asynchronous, etc. In parallel some folks started…
Smart speaker bearing witness in murder trial
In 2017 an Amazon Alexa ‘testified‘ in a murder trial in Arkansas, and is now scheduled to do so in New Hampshire (a double murder!). No word on Siri, Bixby, “OK Google” and their kin. Now, obviously big tech would prefer to keep mum on what they are recording around your house, and a subpoena…