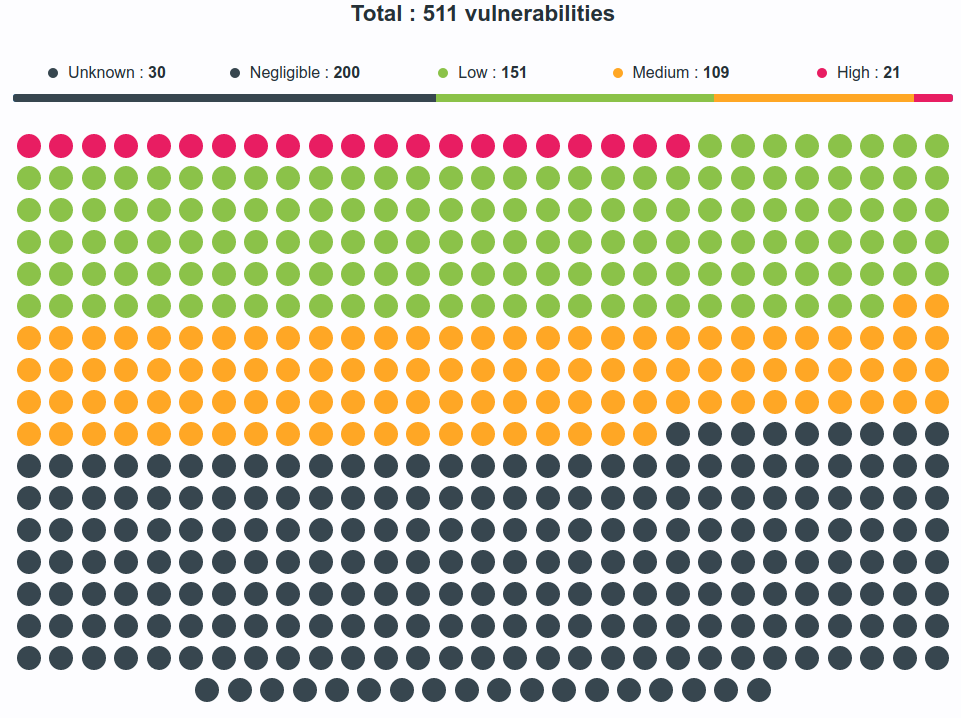
OK, from the previous post you see that I was experimenting with a Static Application Security Testing (SAST) solution. And, I was shocked and appalled by the problems that came from the upstream. See the table below, the dots on the left, each represents a problem. Red means ‘All your bases are belong to us’ for severity.
After about 4 hours of hacking, I have the list on the right (and have examined all the yellows, and found them to be non applicable. But, the left image is what happens when you just write a Dockerfile with a ‘FROM’ line in it from some upstream. And this one is well maintained, others are much worse.
So think of the risk you are importing. 1 line, no oversight, and its rotten to the core.
If you are using a tool like Docker, or a language like Go, you are playing with fire, and you are ultimately responsible for the ‘direct import from source’.
Colour me surprised. I guess the only saving grace is its hard to fingerprint these specific items from remotely, from over the network. But, get a tiny bit of non-privileged local code executing and you can open the door wide and fast.
 |
Leave a Reply