This is not much of a book review. Head over to http://nap.edu/12050 if you want to read this yourself 🙂
If you don’t want to read it, tl;dr: IT insecurity exists in many devices, and some of them control the fate of countries. Earlier I wrote about some of the SCADA problems as found through everyone’s favourite tool Shodan.
There is a concept called ‘critical infrastructure’. Things we need to run out lives. Electricity is one of them. Without it people die, quicky. Hospitals, food safety, transportation, etc.
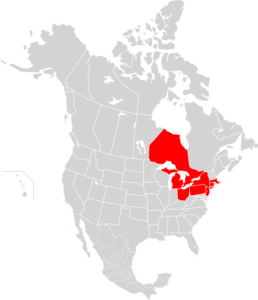
And the power grid is the original distributed network. Many companies all connect to it, and are collectively regulated (in North America under NERC). In 2003 we saw a large scale eastern-seaboard outage. The cause? A software bug in an alarm system in FirstEnergy, one of the many interconnected companies. As power is used, the overhead cables heat and droop, and rebalancing is done to prevent them from drooping too much into trees.
Now, imagine, is this the only software bug? What if others can be exploited, perhaps remotely. That is what this book is about. Physical security (you and a pair of bolt-cutters can be in many power grid areas). Smart-meters, they use wireless IP connectivity. Smart grids will drive when my car charges, and, soon, be able to have me drive power back into the grid. Solar and other local-generation balancing.
Its all a set of software, systems, people. And, any or all of those things can be imperfect.
The 2003 outage had an estimated ‘social cost’ of $4B – $10B. ($8.6B according to this IEEE presentation).
Now imagine the amount of time you spend security your home widgets. Upgrading them. You have done that this week right? Now imagine if you had to climb poles or drive a truck to a remote site to do it. Hmm.
Anyway, read the book, its interesting.
Leave a Reply