OK, not all DNS providers support this. But, if yours does, consider adding a CAA record. What is a CAA record you ask? Its a DNS Certification Authority Authorisation, and its a very simple thing to add and use that increases your security. It allows one to assert, via DNS, which certificate authorities can issue certificates for their domains. Its pretty simple, you add a record like:
example.com. CAA 0 issue "letsencrypt.org"
and call it a day. It can get more complex if you need, e.g. 1 provider for wildcards, one for non, etc. But, for most people, a single record will get them going.
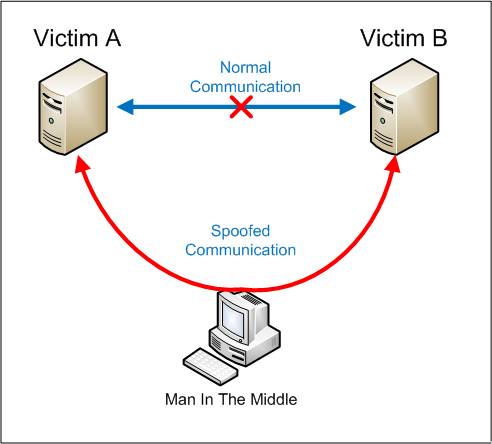
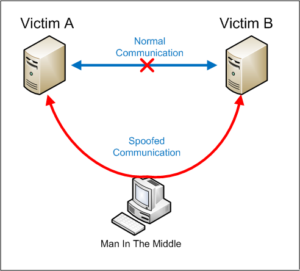
So why would you do this? Well, what if (and not actually if, it has already happened) a certificate authority is compromised? In 2011 an Iranian hacker broke into (a reseller for) Comodo and issued certificates for Gmail, Hotmail, … and then later, another provider. The net effect was a man-in-the-middle compromise.
So, your browser trusts root X & Y, and your site is signed by root Y, you put in a CAA record for Y, and you reduce your risk. if X is compromised, you are still ok.
Leave a Reply