
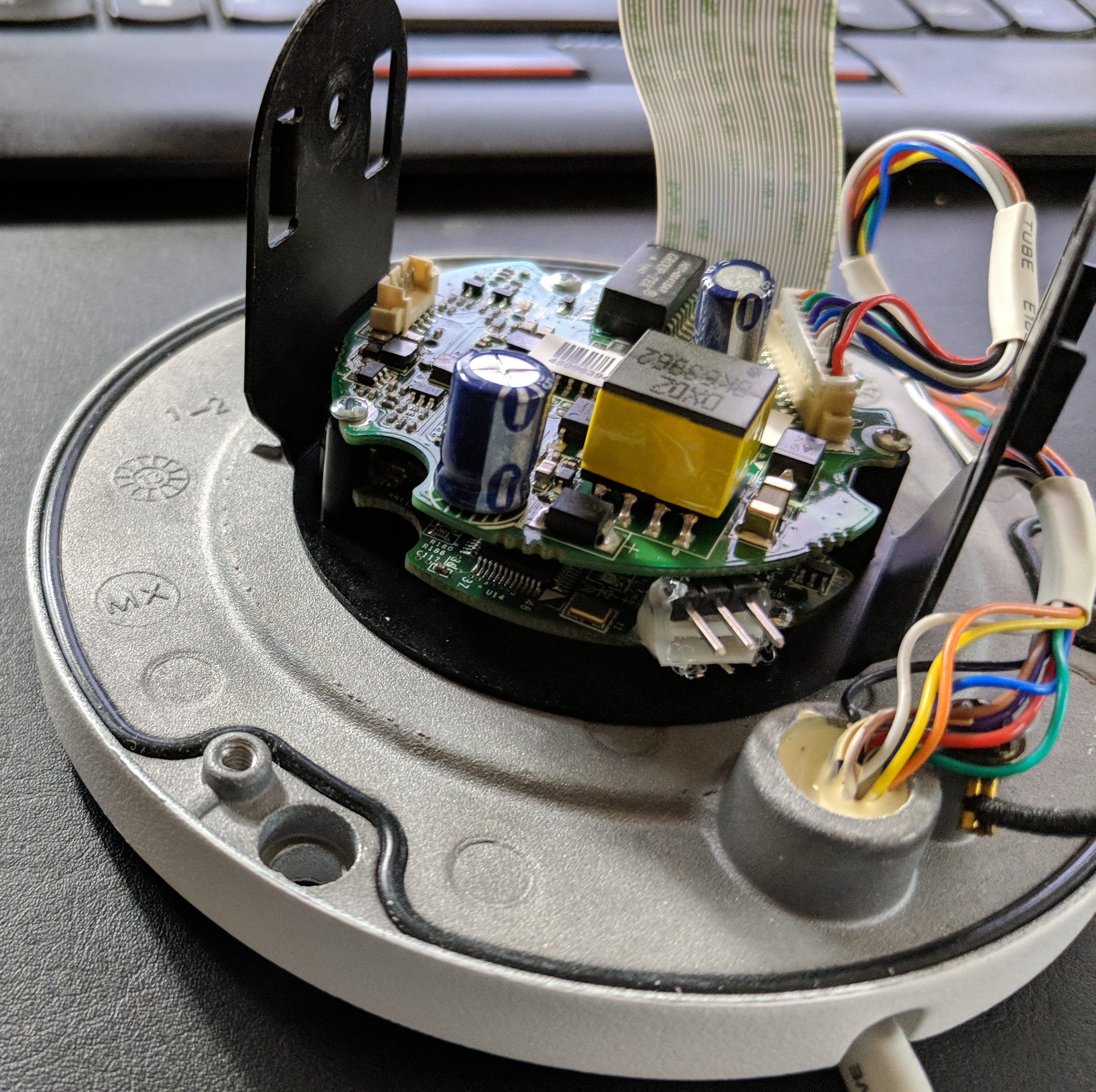
(for those just joining, I have some IOT devices, notably IP cameras, which are now insecure, and there is no, and will be no, firmware upgrade for them from the vendor to resolve, so i have opted to take the path less taken and ‘fix’ them).
The hikvision cameras, like many of these devices run ARM. The first few lines of dmesg (or cat /proc/cpuinfo) tell you what you need to know:
# dmesg [ 0.000000] Linux version 2.6.38.8 (chenyuanming@Cpl-Frt-BSP) (gcc version 4.6.1 (Sourcery CodeBench Lite 2011 [ 0.000000] #18 PREEMPT Thu Jan 21 17:27:08 CST 2016 [ 0.000000] CPU: ARMv6-compatible processor [4117b365] revision 5 (ARMv6TEJ), cr=00c5387f [ 0.000000] CPU: VIPT nonaliasing data cache, VIPT nonaliasing instruction cache [ 0.000000] Machine: Coconut
# cat /proc/cpuinfo Processor : ARMv6-compatible processor rev 5 (v6l) BogoMIPS : 478.41 Features : swp half fastmult edsp java CPU implementer : 0x41 CPU architecture: 6TEJ CPU variant : 0x1 CPU part : 0xb36 CPU revision : 5 Hardware : Coconut Revision : 13ec300a Serial : 0000000000000000
What is also needed is the ABI and libc version:
# /lib/libc.so.6 GNU C Library (Sourcery CodeBench Lite 2011.09-70) stable release version 2.13, by Roland McGrath et al. Copyright (C) 2011 Free Software Foundation, Inc. This is free software; see the source for copying conditions. There is NO warranty; not even for MERCHANTABILITY or FITNESS FOR A PARTICULAR PURPOSE. Compiled by GNU CC version 4.6.1. Compiled on a Linux 3.0.1 system on 2011-12-07. Available extensions: crypt add-on version 2.1 by Michael Glad and others GNU Libidn by Simon Josefsson Native POSIX Threads Library by Ulrich Drepper et al Support for some architectures added on, not maintained in glibc core. BIND-8.2.3-T5B libc ABIs: UNIQUE For bug reporting instructions, please see: <https://support.codesourcery.com/GNUToolchain/>.
So normally I would just do a configure of the toolchain (or use dockcross). But to be certain of matching to get started, we can use the exact binaries they used, from mentor graphics.
OK, lets start by fixing that dropbear (sshd) issue.
First, get the dropbear source.
Then, with the unpacked codesourcery tools on the path, run configure & make:
./configure --host=arm-none-linux-gnueabi --disable-zlib make -j6 PROGRAMS="dropbear dbclient scp sftp dropbearkey dropbearconvert" MULTI=1
now, we’ll strip it, and then run it through my ‘echo -n -e …’ hack from part 1. Now we paste this into the shell, run it, and this gives an output of the new dropbear binary on the device. Check it, it works, great!
Now, we’re going to put this dropbearmulti in /dav/bin, and then add this to /dav/initrun.sh. Their ‘app’ will add a 2nd entry for root, and one for the user you created in the web UI, with hashed passwords and the shell as from this template entry. The echo I put in there to /etc/passwd thus has two purposes: 1) get rid of the hard-coded backdoor password of ‘hiklinux’ and 2) make a template for the subsequent user that I will be able to ssh in as.
# Fix ssh --dab
kill $(ps |awk '/[d]ropbear/ { print $1}')
echo root:*:0:0:root:/root/:/bin/sh > /etc/passwd
/sbin/iptables -F
rm -f /sbin/dropbear*
cp /dav/bin/dropbearmulti /sbin/dropbearmulti
chmod 555 /sbin/dropbearmulti
ln -sf /sbin/dropbearmulti /sbin/dropbear
ln -sf /sbin/dropbearmulti /sbin/dbclient
ln -sf /sbin/dropbearmulti /sbin/dropbearkey
ln -sf /sbin/dropbearmulti /sbin/dropbearconvert
ln -sf /sbin/dropbearmulti /sbin/ssh
ln -sf /sbin/dropbearmulti /sbin/scp
ln -sf /sbin/dropbearmulti /sbin/sshd
mkdir /root/.ssh
chmod 700 /root /root/.ssh
dropbear -ROK, more sadness, they have signed (well, a well known hash) the initrun.sh:
Digest : 0442fdcafa5f2b7beae0d85db18b9ea8482ddc52 Digest : 135691773f8a55a4ad5024cafbf996c861c06d6a pFileDsc=/home/initrun.sh,iRet=-6,data check fail! pFileDsc=/home/initrun.sh,iRet=-6,damage to reboot!
I wonder what this means… It doesn’t *seem* to affect anything.
Towards the end of the script I will patch the language:
# Now patch the language --dab cd /home/webLib/doc/i18n tar zxf /dav/IElang.tar tar xf /dav/IElang.tar en.tar.gz tar zxf en.tar.gz rm -f en.tar.gz rm -rf zh ln -s en zh
Note: you could also change Languages.json in that same dir, and add ‘en’, but I’m not sure what other side affects there are.
But, it seems we are good, now I can reboot (without the u-boot init=/bin/sh hack) and end up w/ a patched dropbear, patched web interface, and ssh access without a well-known password.
Leave a Reply