Month: September 2017
Old School Surveillance?
So this am I look out my hotel window. I’m on a sort of ground-floor/flat-roof thing, w/ a somewhat sketchy patio door leading out. And what greets my eyes? A few cigarette butts, a discarded lighter, and a pair of tighty-whiteys. So, uh, what sort of party was ongoing last night outside my window (long…
Immunising for security? How to create herd immunity for spear-phishing
So I’m reading the disaster that is Equifax/Deloitte/… security hacks. And it got me thinking about how one method we learn is by pain, and another is by vaccination. And maybe that can apply to a corporate learning organisation. First, lets look at some examples. I have a big ugly scar on my arm from…
USB-C portable monitor and Linux play (mostly) nice
Recently I acquired a ZenScreen MB16Ac. Its a single cable (USB-C) 15″ monitor that you travel with. It has a unique feature, it can do USB-C ALT-MODE (e.g. act directly as a monitor), or become USB 3.1 and do DisplayLink (no where near as good). Since my laptop supports ALT-MODE, it works out of the…
Identity theft and safety in numbers. Poe’s purloined letter applications.
There have been a lot of very public hacks recently which made off with entire user databases. The most recent, Equifax, saw hundreds of millions of users have their personal financial information leak online. Ooops. As an end user, you can use best practises (e.g. don’t share passwords across sites, use 2-factor, etc), and still…
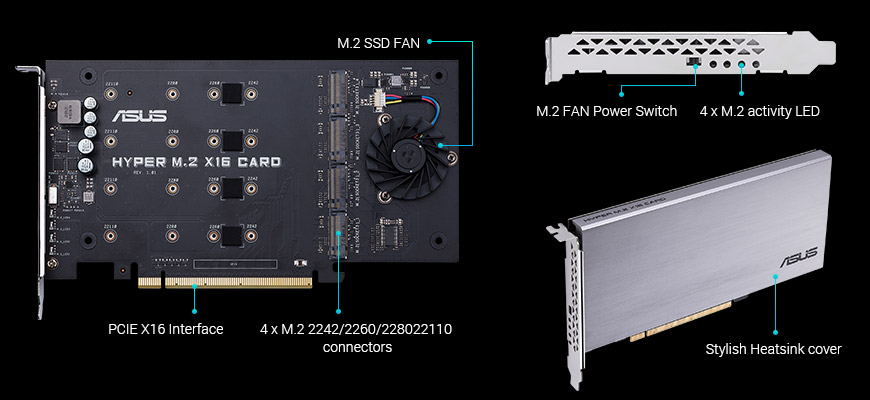
Storage expansion: method chosen, input discarded
[ps a lot of people were asking ‘how do i subscribe to blogs’. The most convenient option I find to aggregate a lot of content is feedly. You make a page there, and it subscribes to all the content from various sources you consume. But you can use any RSS feeder from the main page…