TLS 1.3. Its new, its shiny, its much better.And its supported by nginx 1.13 which is part of the backend of this blog.
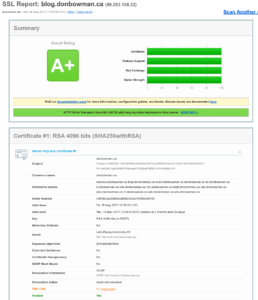
It was a bit of work to get a perfect score on ssllabs test (as below), and here’s how I did it.
First, the server supports a bunch of different ‘sites’ (each is a different host name, and thus a different SNI). I used Let’s Encrypt for the certificates. To make matters simple for config, I created a single include file with all the SSL parameters:
ssl_protocols TLSv1.3 TLSv1.2; ssl_certificate /etc/letsencrypt/live/donbowman.ca/fullchain.pem; ssl_certificate_key /etc/letsencrypt/live/donbowman.ca/privkey.pem; ssl_trusted_certificate /etc/letsencrypt/live/donbowman.ca/fullchain.pem; ssl_dhparam /etc/ssl/certs/dhparam.pem; ssl_ecdh_curve secp384r1; ssl_ciphers 'EECDH+AESGCM:EDH+AESGCM:AES256+EECDH:AES256+EDH:!AES128'; ssl_prefer_server_ciphers on; ssl_session_cache shared:SSL:10m; ssl_session_tickets on; ssl_stapling on; ssl_stapling_verify on; resolver 8.8.8.8 8.8.4.4 valid=600s; resolver_timeout 5s; add_header Strict-Transport-Security "max-age=63073000; includeSubDomains; preload"; add_header X-Frame-Options SAMEORIGIN; add_header X-Content-Type-Options nosniff;
I then included this in each file:
server {
listen 0.0.0.0:443 ssl http2;
server_name blog.donbowman.ca;
include don-tls.conf;
...
like so.
Leave a Reply